HTTP has become the de facto high level protocol on the Internet. As the protocol used for accessing content on the World Wide Web, developers adapted it to carry much more than
just the static text and images of Web pages. It now carries audio and
video streams, can transfer large files, and can even carry application-to-application remote procedure calls (RPCs). Its ubiquity and indispensability make it a prime candidate for tunneling operations.
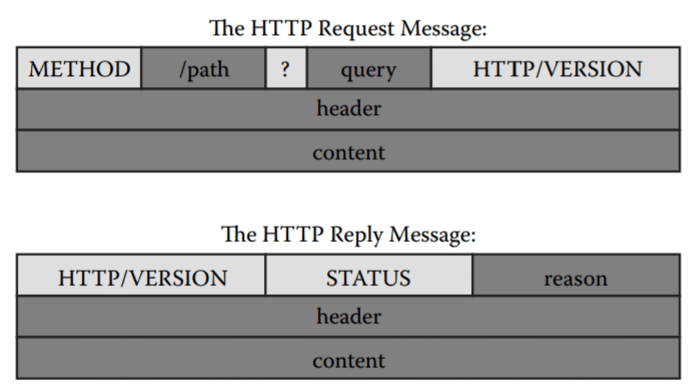
Referring to This picture, in the case of HTTP and most other tun-
nels, other appropriate software that communicates via the protocol of choice simply replaces the client, server, connection, and data (pay-
load). This pic shows the syntaxes of an HTTP request and reply
that illustrate areas of the protocol that can contain discretionary
information for data transfer.
As one can see, the protocol allows, in essence, unlimited space for content (or payload) in the request or reply message in addition to other open areas, such as the headers, whether this content includes arbitrary custom headers or inappropriate data in valid headers. This makes it convenient to transfer arbitrary data to and from an HTTP server. All one needs to tunnel the traffic is software that can pretend
to talk to the protocol but in reality can transfer data for some other
(perhaps nefarious) purpose. A tunneling Web server or a tunneling
Web application running on a legitimate Web server will work. Both
types of solution are readily available as open source software. Since
tunneled traffic looks and acts like HTTP, application proxies are not
a viable defense, as malicious users or software will simply use the proxies as their administrators intended: to transmit HTTP message through a control point.
Most malicious code already acts as a simple HTTP tunnel; in practice, it posts sensitive data to malicious Web servers for purposes other than to retrieve a Web-based resource. It also sometimes communicates over HTTP; however, it may not act as fully functional tunnels that attackers could use to infiltrate or exfiltrate the network on which they sit. To do that, attackers need a complete tunnel client and server. Some common software for the task is GNU httptunnel, JHttpTunnel, and Webtunnel. There are also paid services dedicated to the task so that a malicious user needs only a client, such as PingFu on Art of Ping. Commercial solutions also exist that almost make the practice appear as legitimate and valid solutions for defeating “restrictive” firewalls, such as HTTP Tunnel by netVigilance.
HTTPS, which is HTTP secured over a secure socket layer (SSL) against eavesdropping and tampering, is no different from HTTP except that it makes detection harder. If a malicious actor cannot eavesdrop, he or she does not have a chance to detect known signatures of tunnels. Proxies that support HTTPS through a CONNECT method may actually make matters far worse, as the CONNECT
method simply establishes an arbitrary TCP connection that can send or receive any data.