📣Detecting proxies is difficult and
not always reliable. Since many malicious code authors install custom
proxies and use encrypted or custom protocols, it is very difficult to detect all proxies. There are techniques to detect common proxies, but such techniques are unlikely to be effective against attackers who use proxies aggressively.
Port scanning on corporate networks can identify proxies that listen on default ports. Organizations should also monitor changes to proxy
configuration because such changes could indicate that an attacker
compromised a host. The registry key at HKCU\Software\Microsoft\
Windows\CurrentVersion\InternetSettings, ProxyServer, controls the
proxy settings for Internet Explorer. To detect proxies on the network
with intrusion detection systems (IDSs), organizations may use proxy
rules available from emergingthreats.net. The domain name system blacklist (DNSBL) is one example of a blacklist that allows administrators to block certain proxies.
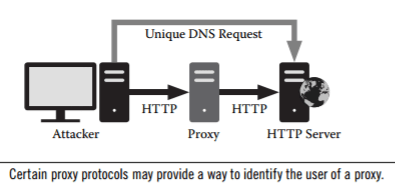
🔦Certain proxies do not proxy all traffic. For instance, a Web appli-
cation can force users to perform unique DNS requests with subdomains. The application links the DNS request to the user’s IP address and verifies that the HTTP request originates from the same IP address. If they are not the same, indicating the use of a proxy, the application can determine that the proxy IP address made the HTTP request and that the user’s actual IP address made the DNS request. Similarly, some Web plug-ins may query the local information rather than using the proxy address. As an example, decloak.net is a Metasploit project that uses the following applicationplugins to determine the true IP address of a proxy user:
• Word
• Java
• Flash
• QuickTime
• iTunes
🔦Metasploit has even provided an application programming interface
(API) for website owners to determine the true IP addresses of their visitors. iDefense configured a browser to use a proxy and showed that the Flash test correctly identified the real IP address because Flash does not use Internet Explorer proxy settings.
🔦More aggressive techniques, such as operating proxies, allow law
enforcement to determine the source and target of attacks that utilize proxies. While such measures are useful, they are generally very
difficult to operate because of abuse. Analysts must carefully monitor activity because attacks now originate from proxy nodes and may result in illegal or otherwise unwanted activity.