Proxies are so common that many attackers scan the Internet for common listening proxy ports. The most common proxies listen on TCP port 80 (HTTP proxies), 8000, 8081,
443, 1080 (SOCKS Proxy), and 3128 (Squid Proxy), and some also handle User Datagram Protocol (UDP). Attackers who install custom proxies often do not use standard ports but instead use random high ports.
Some lightweight proxies are written in scripting languages,which run with an HTTP server and are easier for attackers to modify. Application proxies require configuration. Some applications either do not operate correctly through proxy services because the proxy server removes necessary information or cannot satisfy the request. Some services like The Onion Router (Tor)2 also give users the ability to proxy traffic and hide their original location from victims.
A virtual private network (VPN) acts as a more versatile proxy and support more security features. Instead of configuring the application to use a proxy, users can tunnel all traffic through the VPN. VPN services usually support strong authentication and are less likely to leak information that could identify the user of a proxy.
Attackers commonly use free or commercial proxies (e.g., SOCKS
and VPN) that operators advertise on hacking forums. Attackers may prefer these services to public proxies because they advertise anonymity and claim they do not keep logs, unlike Tor, where community
operators can monitor traffic going through an exit node that it controls. Proxy services that keep logs are a danger to attackers who use these services for conducting fraud and can lead to their arrests.Some commercial VPN and SOCKS proxy services include…
• hxxp://secretsline.net
• hxxp://vpn-secure.net
• hxxp://thesafety.us
• hxxp://5socks.net
• hxxp://vpn-service.us
• hxxp://vip72.com
• hxxps://www.cryptovpn.com
• hxxp://www.vipvpn.com
• hxxp://openvpn.ru
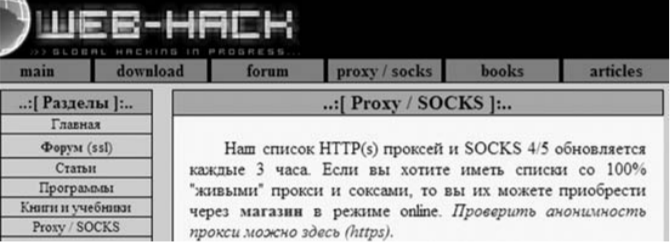
Another example of such a service from web-hack.ru shows free and commercial proxies that are available Translated from Russian, these free Proxy and SOCKS services are updated every three hours; users can also purchase proxy access through
the store. Attackers may prefer proxy services advertised on hacking forums because they are less responsive to abuse requests. For
example, commercial proxy services like FindNot keep logs of their users for a maximum of five days to protect the system from being used for abusive purposes, while many of those services advertised on hacking forums do not keep any logs. Operating proxy services is not illegal because it has legitimate purposes related to anonymity for users; however, some commercial proxy services are more willing to respond to abuse than others.