Type of Firewalls
Packet-Filtering Firewalls:- The most rudimentary of firewalls is the packet filtering firewall. Packet filtering firewalls work at the IP level of the network. Most routers integrate this type of firewall to perform basic filtering of packet based on an IP address. The principal behind packet filtering firewalls is that the firewall bases the decision to allow a packet from one network into another network solely on the IP address of the source and destina- tion of the packet. For instance, if the firewall administration defines the following packet-filtering rules, and if a packet from host 1.1.1.1 is destined for host 2.2.2.2, the firewall allows the packet to pass.
ALLOW host 1.1.1.1 to host 2.2.2.2 Deny ALL
On the other hand, if the packet originated from 2.2.2.2 with destination of 3.3.3.3, the firewall would stop the packet from traversing the network any further due to the DENY ALL rule. Generally, firewalls contain an implied DENY ALL rule. If the administrator fails to include the DENY ALL rule, the firewall, after exhausting all of the rules in the filter set, will default to the DENY ALL rule and deny the traffic, since it didn’t match any defined rule.
Packet-filtering firewalls can also expand on the basic principle of the IP-address-only filtering by looking at the transmission control protocol or user Diagram protocol source and destination port. in this mode, the firewall operates in nearly the same fashion as the packet-filtering firewall the source IP and port and the destination IP and port must match at least one rule in the filter list. More advanced routers and even some higher end switches offer this functionality.
ALLOW host 1.1.1.1 to host 2.2.2.2 DENY ALL ALLOW host 3.3.3.3 to 1.1.1.1
In this example, the firewall administrator has placed an ALLOW rule after the DENY ALL rule. This situation would prevent the processing the last ALLOW rule.
Stateful Firewalls:- Simple packet filtering firewalls suffer from one significant downside: they do not take into consideration the state of a connection, only the endpoint of the connection. Stateful firewalls allow only properly established connection to traverse the firewall’s borders. While Packet filtering is still a key element of these firewalls,the firewall also pays attention to the state of the connection.
Once the firewall allows a successful connection between two hosts using the three-way TCP handshake, the firewall records the occurance of a valid session between the two hosts. If an attacker attempts to generate an invalid session,such as by sending an ACK prior to sending a SYN, the firewall identifies the packet as an invalid state and subsequently blocks the connection. After a host establishes a valid session however, communication between the two hosts can occur unrestricted and without requiring the firewall to return the list of packet filters.
It is the ability to determine the order and state of a communication session that allows stateful firewalls to make faster determinations about incoming packets. Of course, it is important that these firewalls do not run out of memory from storing the state connection. To avoid this problem, stateful firewalls will purge state information for session that have “gone quiet” for a significantly from either host will result in the firewall verifying the packet against packet-filtering rule and the establishment of a new session.
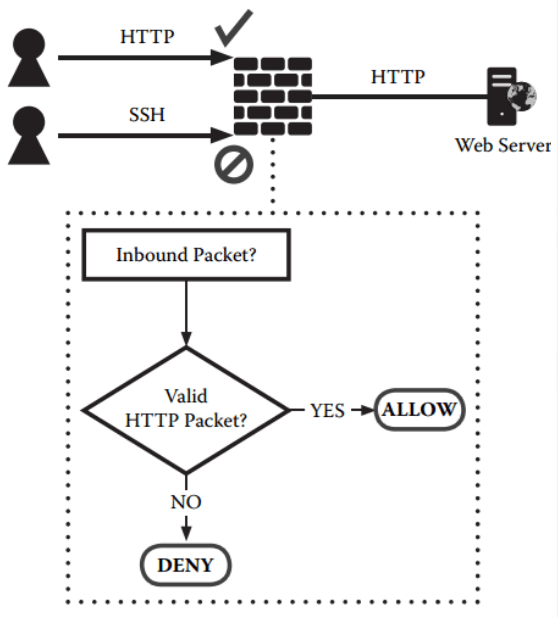
Application Gateway Firewalls:- Application gateway firewalls, also known as proxies, are the most recent addition to the firewall family. These firewalls work in a similar manner to the stateful firewalls,but instead of only understanding the state of a TCP connection,these firewalls understand the protocol associated with a particular app- lication or set of applications. A classic example of an application gateway firewall is a web proxy or e-mail-filteting proxy. A Web proxy, for instance, understands the proper HTTP protocol and will prevent an improperly constructed request from passing based on predefined condition or heuristics.
These proxies also prevent unknown protocols from passing through. For Example, a properly configured HTTP proxy will not understand an SSH connection and will prevent the establishment of the connection. This level of packet inspection cannot occur with either a packet filtering or stateful firewall, as neither firewall type look at the application layer of the network stack. By identifying improperly construct Packet for a given protocol, the application gateway firewalls may prevent some types of protocol specific attacks; however, if a particular protocol’s definition allows for such a vulnerability, the gateway will provide no protection.