🔦The DNS stores information in Resource Records (RR). these records are separated by type, and each one stores different information about a domain. RFC1035 defines the variety of different RR types and classes, including the most common types: A, NS, and MX.¹¹ An A record maps a domain to an IP address. NS records provide the name of the that domain’s
authoritative name server.The NS record includes an additional section with the type A records for the name servers so the resolver can easily contact them. The MX records refer to mail exchange domains used to send e-mail over Simple Mail Transfer Protocol (SMTP). Like anNS record, MX records include an additional section to provide type A records to the domains included in the MX record. The following is an example
of a query for the http://www.google.com A record and the resulting answer.
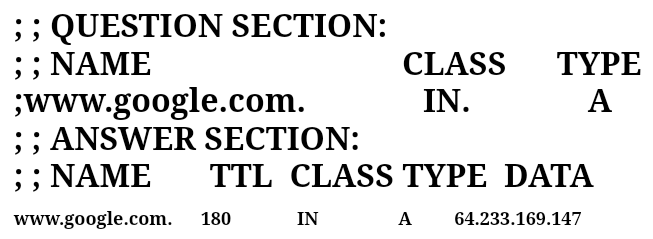
In the question section, the resolver has specified that if wants the A record for http://www.google.com in the Internet class (specified by IN).During the development of DNS, additional classes were created, but the Internet class in the only one commonly use today.The answer session includes the information from the question, the IP address for the domain, and a time-to-live (TTL) value. The TTL
specifies the number of seconds for
which the data in the record are valid.
This value is the key to the catching
system described above; as without a
TTL, the servers would not know how
long any particular data could be cached.
Security and the DNS As a fundamental part of the modern Internet, the security of the DNS is important to all Internet users. In the previous discussion of how the DNS system works, it is important to note that no authentication of result ever occurred. This makes the system
vulnerable to an attack known as DNS cache poisoning, where in an attacker
tricks a DNS server into accepting data from a nonauthoritative server and returns them to other resolvers.
Extensions to the DNS protocol,known as DNSSEC, solve this problem using
cryptographic keys to sign RRs. While
this system has not yet been widely
adopted, VeriSign, the company
responsible for management of the root domain, deployed DNSSEC for the root DNS servers on July 16, 2010. This is n important step in the deployment of DNSSEC as it provides a single trust
anchor that other domains can use to
streamline deployment. Protection of
credentials used to manage domain with registrars is also key to the security ofthe DNS.In December 2008, attackers gained access to the credentials that control many domains, including and used them to all install a banking Trojan on visitors’ system.Legitimate use of DNS also has implications for security professionals.Fast-flux networks rely on very short DNS TTL values to change the IP address associated with a domain rapidly. Phishing attacks that employ domain name similar to those registered by financial institution also employ the DNS. Attackers can exploit the length of a
domain name to create phishing domain that mimic legitimatebanking domainsto steal information.This pictures shows a five-level domain of the online.citibank.com.n5mc.cn that may appear to belong to CitiBank but is actually a subdomain of n5mc.cn.
Organization that want to issue takedown requests for these domains need to understand how the DNS works so they can take the correct actions.
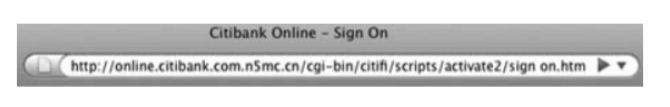
A long phishing domain appearing to belong CitiBank.