Cryptography
📣This blog provides information on Basic cryptography to explain the history and basic of ciphers.
📣The English word cryptography derives from Greek and translates roughly to “hidden writing.” For thousands of years,groups who wanted to communicate in secret developed methods to write their messages in a way that only the intended recipient could read. In the information age Almost all cryptography has advanced.
📣Understanding how cryptography work is important for anyone who wants to be sure that their data and communications are safe from intruders.This blog Discusses cryptography, starting with Basic ciphers and cryptanalysis.
👉This ancient Egyptians began the first Known practice of writing secret msg, Using nonstandard hieroglyphs to convey secret msg as early as 1900 be.Since that time, people have developed many Methods of hiding the content of a msg. These methods are known as ciphers.
🔦The most famous classical ciphers is the Substitution cipher.Substitution cipher Work by substituting each letter in the alphabet with another one when writing a msg. For instance, one could shift the letters of the English alphabet as:-
abcdefghijklmnopqrstuvwxyz
zxcvbnmpoiuytrewqasdfghjlk
Using this cipher, the msg “The act starts at midnight” would be written as “gur np finger no zvqavtug. ” The text above,show How to decode msg, is known as the key. This is a very simple substitution cipher Known as the Caesar cipher or ROT13 Because the characters in the key are rotated thirteen spaces to the left.
🔦Cryptography is driven by the constant struggle between people who wants to keep msg secret n those work to uncover their meanings. Substitution cipher are very vulnerable to cryptanalysis,the practice of breaking codes. With enough text, it would be simple to begin replacing characters in the cipher text with their possible cleartext counterparts. Even without knowing about the Caesar cipher, it is easy to guess that a Three-letter word at the beginning of a sentence is likely to be the. By replacing All instance of the letters d, p, nd b With t,h, nd e, the ciphertext changes to…
the npt ftnetf nt zvqavtht
Next, the analyst might notice that the
fourth word is only two letters long n
ends with t. There are two likely possi-
bilities for this word: rt and it. He chooses at nd replaces all occurrences of n in the sentence with an r.
the rpt ftretf rt zvqavtht
With rt in place, the pattern is clearer, n the analyst guesses that if the letter g translates to m, the adjacent letter f may translate to n.
the rpt ntretn rt zvqavtht
The word ntr_tn now looks very closely. to ntretn, and the analyst make.another Substitution, indicating that rst is equivalent to asd, Which reveals the full pattern of the cipher n the msg. While the msg is now clear, the meaning of “the act starts at midnight” is not.Code word are an excellent way of hiding a msg but unlike cryptography, can’t hide the
meaning of arbitrary information without agreement on the meaning of the Code words in advance.
🎤THIS SURPRISE FOR YOU::–
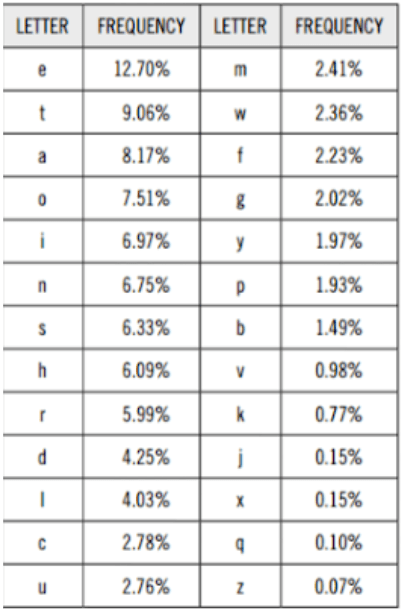
In this surprise, Use of psychological principal. What we have thoughts in our mind n what we are write in our chats,article,password… .
#TWO ADVICE#
1.Not to use large frequency latter in
your password.
2.Always change your password with-
in 15 days.