“cyber security funda”
––––––––––––––––––––––––––––––––––––
📣Network and Security Concepts:
🔦Information Assurance Fundamentals:-
➡️Authentication, authorization, and nonrepudiation are tools that system designers can use to maintain system security with respect->confidentiality, integrity, and availability.
➡️There are three key concept,known as the CIA triad, which anyone who protects an information system must understand: confidentiality, integrity, and availability.
🔦Authentication:-
➡️Authentication is important to any secure system, it the key to verifying the source of a msg or that an individual is whom he/she claims.
🎤Factor of authentication-
👉Something You Know:- information the system assumes others don’t know; this information may be secret, like a PW or PIN code, or simply a piece of information that most people don’t know, such as user’s mother’s maiden name.
👉Something You Have:- Something the you see possesses that only he/she holds; a radio frequency ID (RFID) badge,one-time-PW generating token, or a physical key.
👉Something You Are:- A person’s Fingerprint, voice print, or retinal scan—factors known as biometrics.
🔦Authorization:-
➡️The NIAG defines authorization as “access privileges granted to a user, program, or process”.
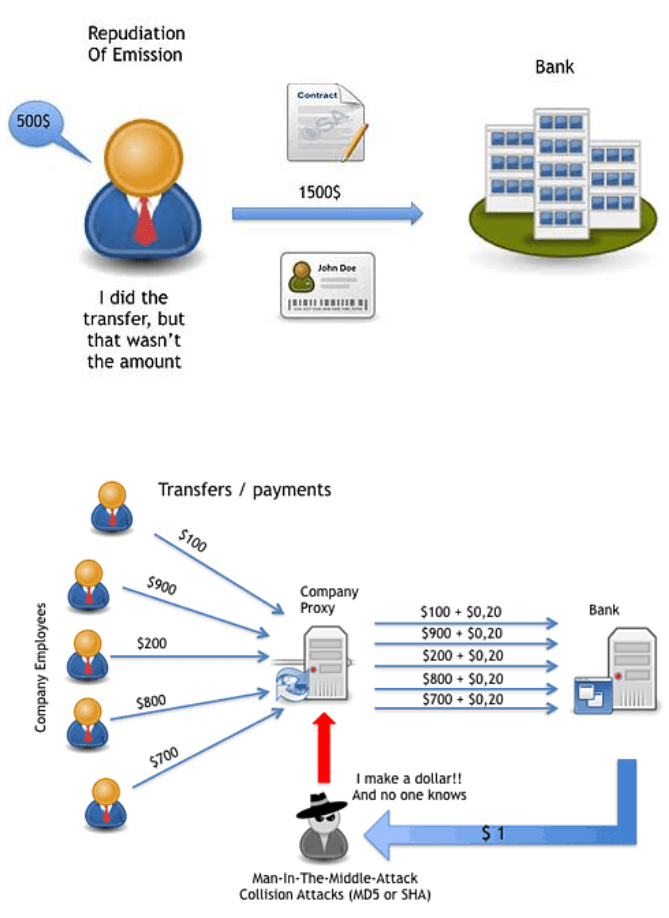
🔦Nonrepudiation:-
➡️Imagine a scenario wherein Alice is purchasing a car from BOB and signs a contract stating that she will pay $20,000 for the car and will take ownership of it Thursday.if Alice later decides not to buy the car, she might claim that someone forged her signature and that she is not responsible for the contract.To refute her claim, BOB could show that a notary public verified Alice’s identity nd stamped the document to indicate this verification.In this case, the notary’s stamp has given the contract the property of nonrepudiation.
🔦confidentiality:- The term confidentiality is familiar to the most people, even those not in the security industry. The NIAG defines confidentiality as “assurance that information is not disclosed to unauthorized individuals, processes, devices”.
🔦Integrity:- In the information security re-alm, integrity normally refers to data integrity, or ensuring that stored data are accurate and contain no unauthorized modification
🔦Availability:- Information systems must be accessible to users for these systems to provide any value. IF a system is down or responding too slowly, it can’t provide the service it should. In Short availability is, “full data and information timely provide for authorized.
